World's Most Sophisticated
AI Agents Native GRC Platform
40x speed, 20x scale against status quo!
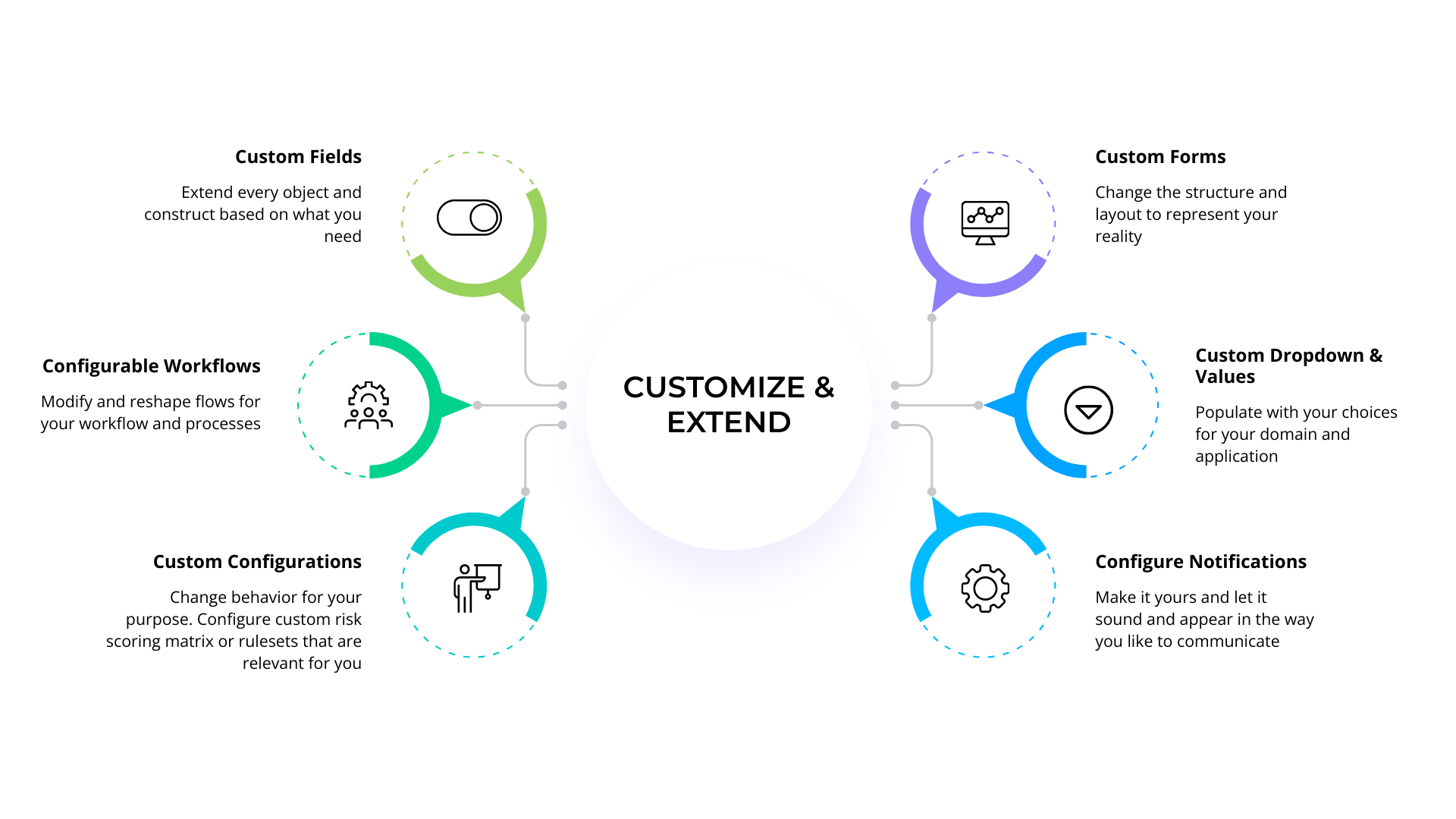
Get the Uno Advantage!Service as a Software (Platform)
Get enhanced productivity at scale, while savings costs
Get the Uno Advantage!Enterprise Ready AI
Banking, Healthcare, & Fortune 1000 Trust it
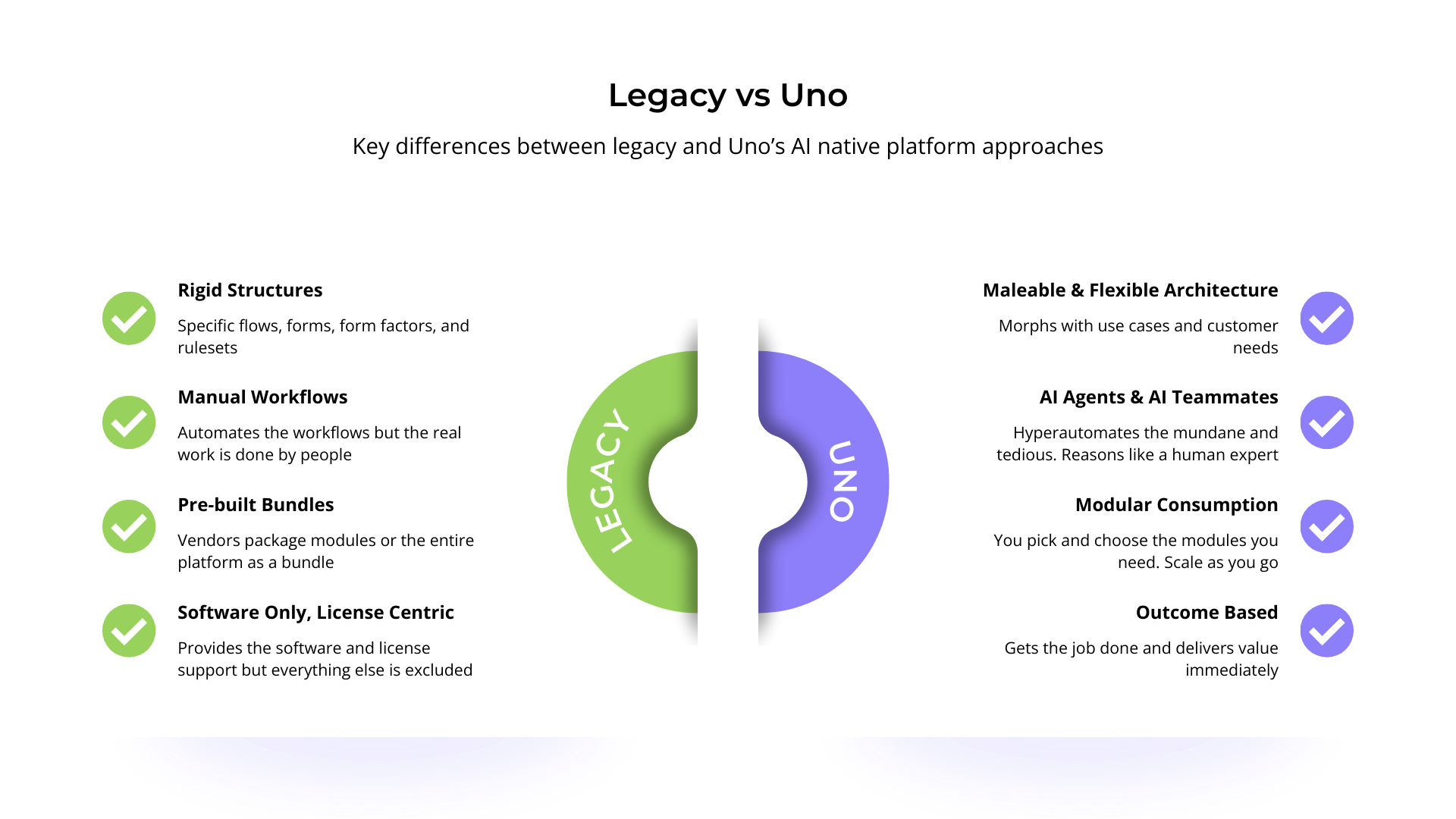
Reliability, dependability, and customizability to transition from legacy to an AI enabled future.
Get the Uno Advantage!
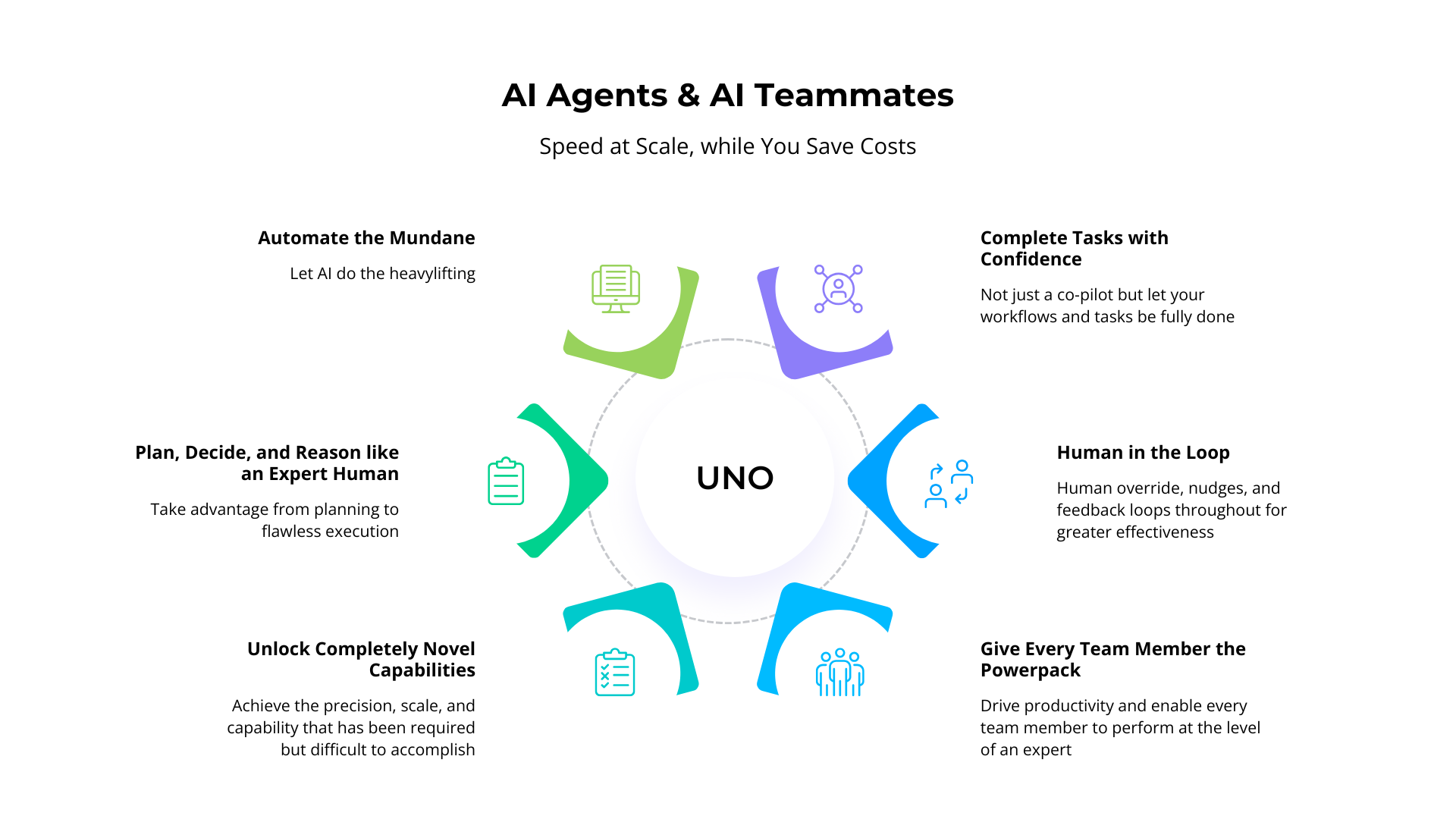
AI Agentic Platform to enhance productivity, while saving costs!
Increase accuracy, scale, and speed with the world's most comprehensive and sophisticated modern GRC platform.
- Move from mundane manual work to AI doing the work for you.
- Scale your team, with AI teammates.
- Go from expensive & slow risk and compliance management to fast, efficient, & effective coverage.
Enterprise ready AI platform that assures reliability, consistency, dependability, and explainability while delivering outstanding features and capabilities. Reason why banking, financial services, healthcare, and enterprises love Uno!
Uno Advantage!
Comprehensive full featured state of art platform for Governance, Risk, Compliance, & Resilience
Ensure compliance with confidence
Regulatory compliance, certifications, and attestations made easy, without compromising on quality or scope.
- Autonomously run comprehensive coverage & gap analysis in an instant
- Comply across multiple frameworks & standards, without the duplication of effort
- Continuously pass all tests of design & operational effectiveness
Measure, Quantify, Treat, and Manage All Risks
Accurate and effective measurement and assessment across structured and unstructured risk management initiatives.
Use AI to autorank and quantify risk assessments. Dig deep into documents and data to analyze and measure the risk hidden in operational details.
Run Assessments & Comprehensive Audits
Maturity assessments, risk measurement efforts, and internal audits made simple, effective, and fast with greater coverage and higher accuracy.
- Collect, assess, quantify, and classify responses & evidence accurately, at scale.
- Transition from automated collection to autonomous analysis.
- Reduce effort, reuse evidence, and automatically crosswalk.
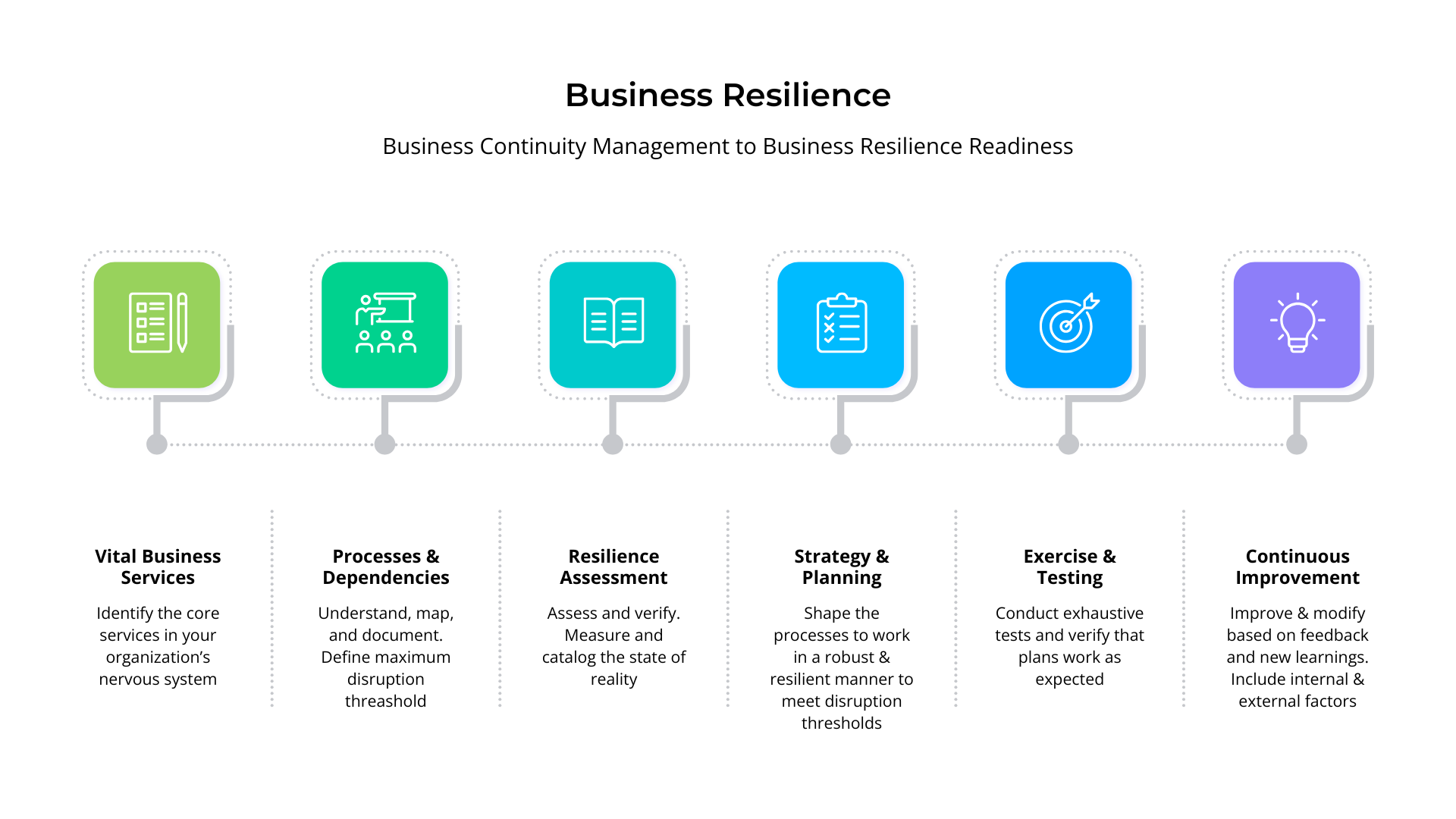
Enable Business Resilience
Robust governance, risk management, and compliance. Ensure business resilience, reduce costs, and improve operational efficiency.
Use AI Agents for comprehensive, accurate, and integrated risk management and business impact analysis. Ensure continuity and resilience with confidence.
